The Security Alliance (SEAL) team conducts simulated, but realistic protocol attacks to prepare teams for worst-case scenarios. However, instead of wreaking havoc and causing panic, the SEAL drills are tactical preparations designed to help protocol teams identify dependencies, understand internal processes, and improve their incident response procedures.
From conducting an initial analysis to executing a simulated D-Day scenario, the SEAL team has a set process in place. Let’s drill down into the SEAL drills. 🪖
Mission objectives
The goal of the SEAL drills is to help protocol teams prepare for emergency situations in a realistic way. The drills help teams practice their incident response, including detecting a problem, diagnosing its cause, and responding in a quick and organized manner.
The drills entail conducting simulated scenarios on Tenderly Virtual TestNets. Since Virtual TestNets replicate the state of a production network, teams can deal with realistic scenarios and respond as if they were actually happening on-chain.
By going through several well-defined steps, teams can understand the extent of external dependencies that make their protocols vulnerable. They can also practice and improve their emergency procedures so they can mitigate any risks in the quickest way possible.
The operation: What the drill process looks like
The SEAL drills consist of three phases, each one with a clear goal and a set of steps:
Reconnaissance
During the first phase, the SEAL team carefully analyzes the protocol and the protocol team’s procedures. They examine all open-source resources, documentation, and public communication. This phase is essential for crafting a scenario that best suits the team and covers all the bases.
By performing an in-depth analysis, the SEAL team can fully understand the breadth of a protocol. They try to identify all external dependencies (e.g. oracles), whether the protocol has multiple versions or any planned upgrades, and whether it was a target of any previous attacks.
Tabletop simulation
A tabletop simulation is the second phase of a SEAL drill. During this step, the SEAL team has an open discussion with the protocol team. They go over several different scenarios, trying to understand how the protocol team responds in a time-sensitive situation, their division of responsibilities, and their general approach to handling emergencies.
This step helps SEAL go over the data gathered in the previous phase and start planning the live drill. This phase also allows both teams to determine the focus of the drill, such as testing a specific part of a protocol.
D-Day: Live exercise
After fully understanding the protocol and the protocol team’s internal processes, SEAL starts preparing the live drill exercise. They set up a few essential infrastructure components and then test and validate the drill before organizing the live exercise.
The live exercise entails organizing a real-time war room and conducting a simulated attack on Tenderly Virtual TestNets, virtually operated networks based on live production data. Virtual TestNets allow SEAL and protocol teams to test actual smart contract and protocol interactions in real time.
This way, the protocol team can practice their emergency response, including both dealing with the attack and internal and public communication. Ultimately, the goal is to help the protocol team strengthen and improve their incident response procedures so they become routine. All the while, SEAL team members are in the trenches with the protocol team, guiding them and providing helpful information.
Behind the lines: How the SEAL team prepares the drills
When preparing a scenario for a protocol attack, the SEAL team has a template in place. However, they always perform certain modifications to make sure the scenario suits the unique needs of each protocol team. For instance, when conducting a Yearn drill, SEAL tailored it to include the interface Yearn engineers normally use for monitoring pools.
Here are the steps the SEAL team follows when preparing drill scenarios:
Validating assumptions and writing tests
First, SEAL wants to understand administrative controls and protocol contracts so they can write appropriate scenarios. They start by listing and validating all assumptions about a protocol.
The team tests and validates assumptions through example scenarios. For instance, they simulate gaining control over an EOA and submitting a malicious transaction. This way, they can monitor what happens with a protocol. This internal testing is done using Hardhat or Foundry on a local fork.
Creating the orchestration script
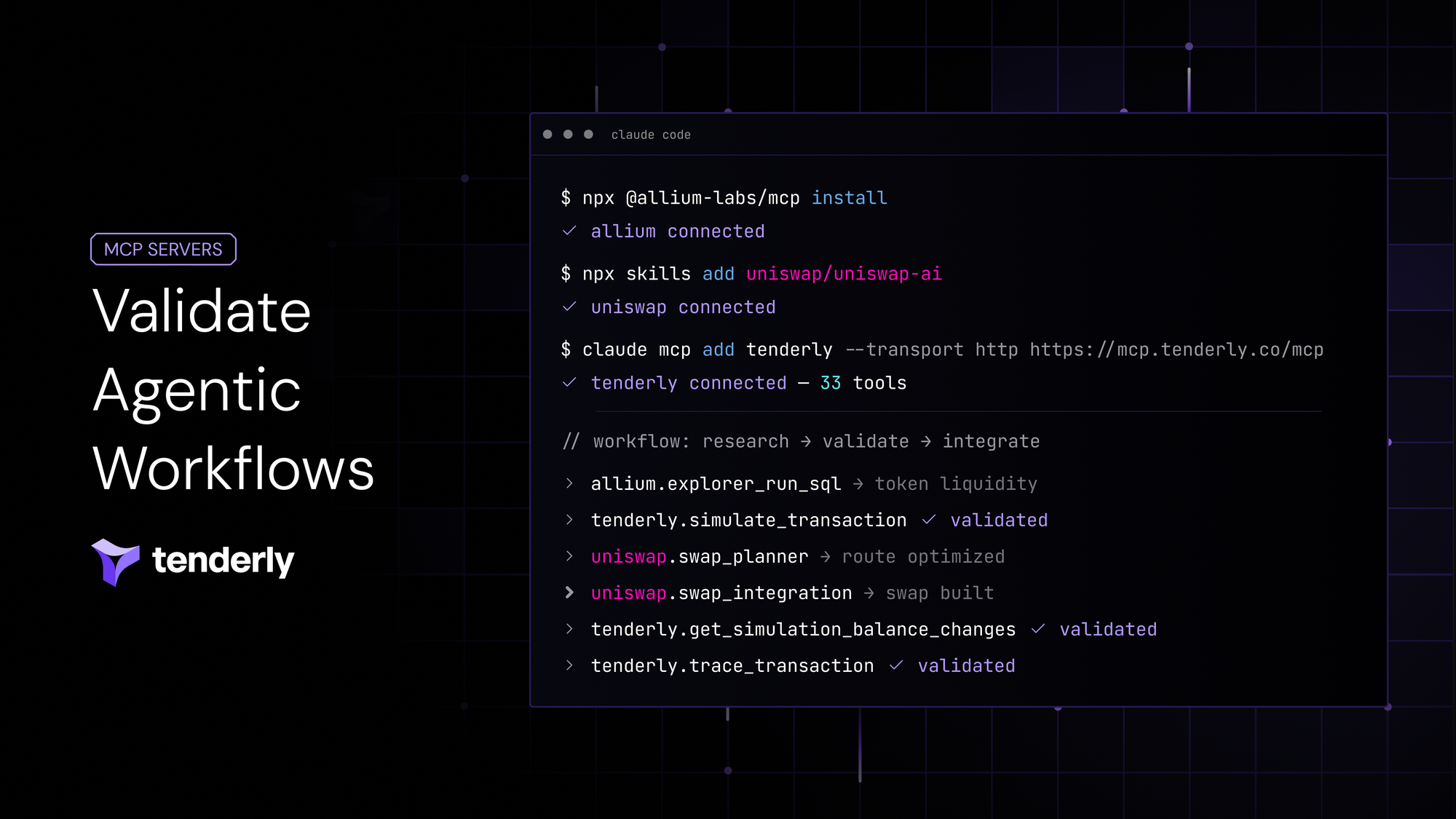
Once all internal testing is completed and the SEAL team confirms all assumptions are correct, they write an orchestration script for running a scenario. They migrate scripts and utilities from Foundry or Hardhat to Silverback. SEAL uses Silverback to create bots that interact with a protocol, impersonate accounts, and handle monitoring.
During this step, SEAL sets up the scenario end-to-end to prepare for the live exercise. They also establish Telegram channels for monitoring and alerting, sending relevant alerts to teams to help with incident diagnosis and resolution.
Setting up a network replica with a block explorer
To run simulated attacks based on realistic conditions, SEAL uses Tenderly Virtual TestNets. The team sets up a Virtual TestNet to replicate the state of a specific network relevant to the protocol. This way, they can play out any scenario on top of production data, yet in a simulated environment with a built-in faucet.
Additionally, a Virtual TestNet comes with a block explorer and debugging tools, giving protocol teams complete observability over simulated transactions. They can examine transactions trace by trace, as well as dive into transferred assets, emitted events, and state changes.
With everything in one place, protocol teams can easily analyze and detect suspicious transactions and then jump right into debugging them. Plus, since most protocol teams use Tenderly in their day-to-day operations, having access to the same tools during the live exercise makes it feel realistic. This way, they can react quickly in time-sensitive situations and mitigate any potential losses.
Get mission-ready for critical situations
SEAL drills help protocol teams prepare for the worst-case scenario and respond quickly to mitigate risks without panic. Such extensive procedures leave nothing to chance, making sure simulated attacks are as realistic as possible. SEAL achieves this by having a strong underlying infrastructure, such as Tenderly Virtual TestNets that replicate production conditions and provide complete observability over simulated transactions.
Ensuring protocol and team resiliency is essential in the Web3 space where stakes are high and exploits lurk around every corner. As Samczsun says, “In a war room, every second counts.”